If you do REST, you probably have a favorite REST client testing tool.
Mine is Postman, a Google Chrome app.
Postman has a nifty feature called Pre-request scripts, which allows you to write some Javascript code that performs a calculation and then reads and writes the “environment” object for the request. This means you can calculate … hashes or digests or signatures or anything you like.
Here’s an example of a script that calculates an HMAC-SHA256 HttpSignature, using the keyId and secret-key embedded in the environment. It also computes a digest on the message payload. Postman helpfully includes CrytoJS in the JS sandbox, so it’s easy to do HMAC and SHA.
In this particular case, the HttpSignature verification on the server requires 2 headers (date and digest) plus the ‘(request-target)’ value. The digest is a SHA-256 of the payload, which is then base64 encoded.
Anyone can start with this and modify it to do other variations.
Good luck!
Addendum
I should have mentioned this: Postman, even the latest Chrome app version, uses XmlHTTPRequest to send out requests. XHR is purposefully limited, in the specification, to restrict some headers from being set explicitly on outbound requests. The list of restricted headers includes: Origin, Date, Cookie, Via, and others. The reason for this restriction: it is desired that the user-agent be fully in control of such request headers.
My example above uses an HttpSignature that signs the Date header. This means the code must also SET the Date header to a known value; in my case I am using a value generated by the pre-request script.
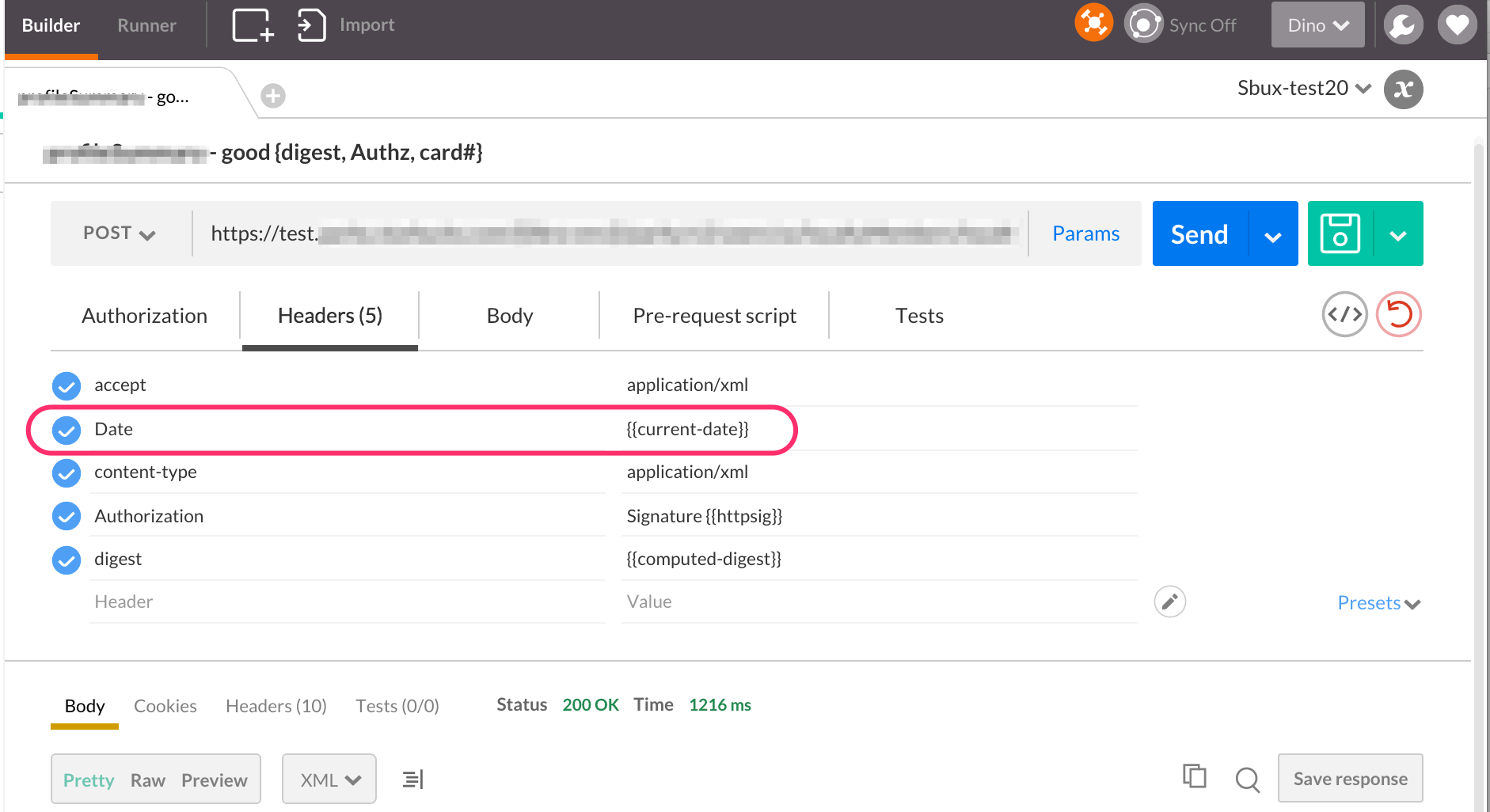
The value corresponds to “now”, the current moment. But the point is the value has to be absolutely known.
This is not possible in standard Postman, because of the XHR restriction. The effect you will see is that the intended Date header silently does not get sent with the request.
This may confound you if you don’t have an ability to trace the request on the receiving (server) side. In the context of a request that uses HttpSignature, the server will throw an error saying “Missing Date header”.
But! in Postman v0.9.6 and above, it is possible to configure Postman with something the Postman people call “the Intercptor plugin”, which then allows the lifting of this restriction. The Date header gets sent, and everything works.
If you don’t want to rely on the Interceptor plugin, and you want the HttpSignature to include the date value, then you’ll have to use a differently named header to hold the date. Use X-Date or anything other than “Date”. You need to change the client as well as the server of course, to make everything hold together.
Zech 2017-February-14
Thanks for this post. It helped me to test my API using post man.
dpc 2017-March-2
Thumbs up, Zech!
Dheeraj Sehrawat 2017-April-2
Hello dpc,
While running it. I am getting the following error
Evaluator.js:246 TypeError: Cannot read property ‘length’ of undefined
at init.concat (all-crypto.js:8)
at c.hasOwnProperty.c.init._append (all-crypto.js:11)
at c.hasOwnProperty.c.init.finalize (all-crypto.js:12)
at Object.SHA256 (all-crypto.js:12)
at eval (eval at loadCustomFile (Evaluator.js:242), :44:29)
at eval (eval at loadCustomFile (Evaluator.js:242), :67:3)
at r.loadCustomFile (Evaluator.js:242)
at Evaluator.js:219
dpc 2017-April-24
Jeez, I don’t understand where you would be seeing that stacktrace. Can you provide some additional context?
Kentaro 2017-September-12
Hi, dpc.
I just run into the same issue. What I found is that if you are trying to do a GET, the request.data is an empty object.
That is why, the line:
var sha256digest = CryptoJS.SHA256(request.data);
fails with: “Cannot read property ‘length’ of undefined”.
For the other verbs, the code is working flawlessly.
Do you have any idea on how to fix this in the
dpc 2017-October-2
Yes – good catch. I think you could solve this via this change:
var sha256digest = CryptoJS.SHA256(request.data || ”);
Giri 2020-January-23
I got message like “cannot read property Sigbytes of undefined”
can you pls help one this to fix it.